Identity Access Management
Comprehensive Identity Governance and Access Control
Uqudo’s Identity Access Management (IAM) solution provides a unified platform for managing digital identities and controlling access to resources across your organization.
Key Capabilities
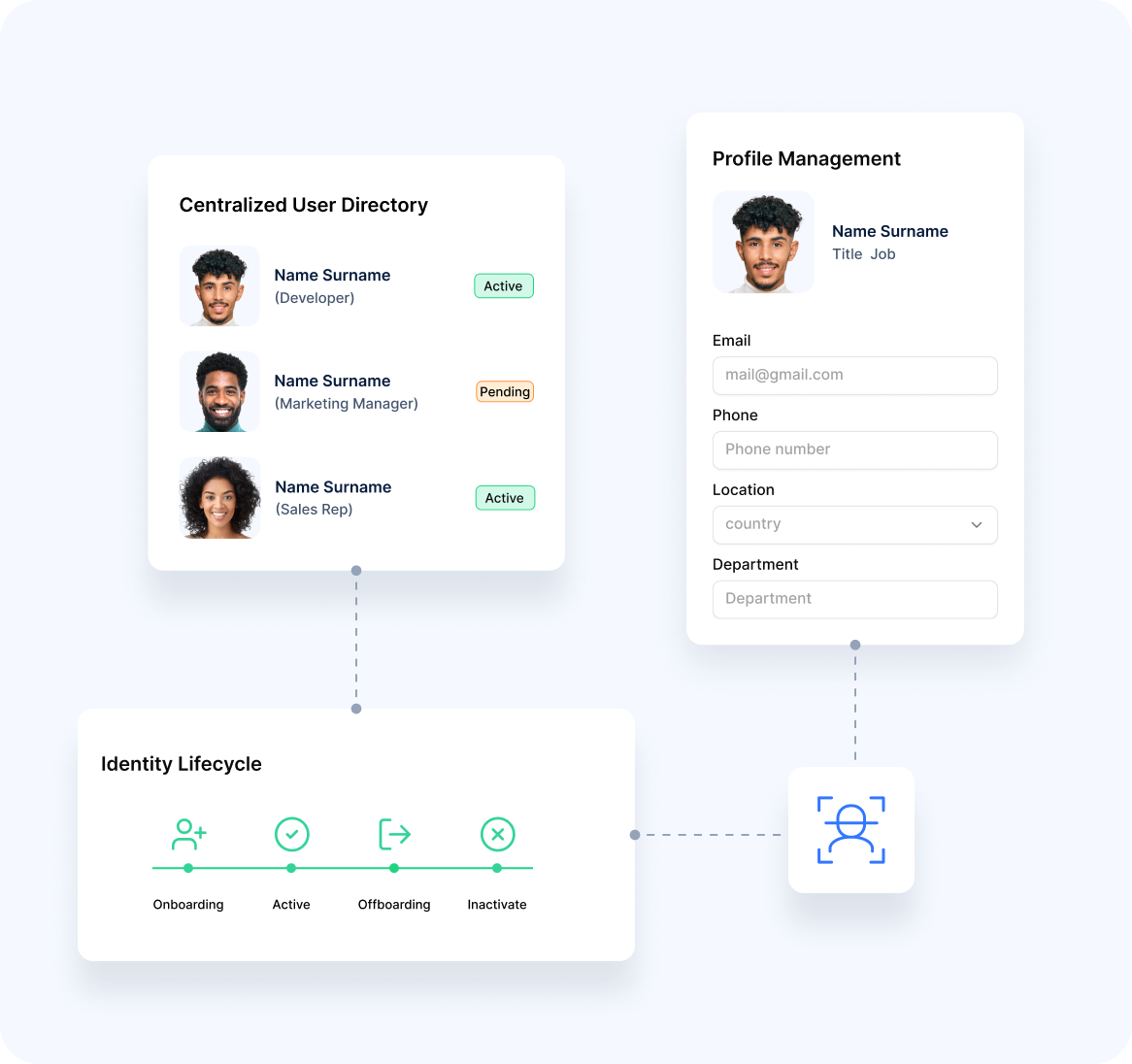
Unified Identity Management
Our platform provides comprehensive identity administration:
Identity Control
- Centralized User DirectoryConsolidated repository of digital identities
- Identity Lifecycle ManagementEnd-to-end administration from creation to retirement
- Profile ManagementMaintenance of comprehensive user attributes
- Self-Service CapabilitiesUser-driven profile updates and access requests
- Directory IntegrationConnection with existing identity repositories
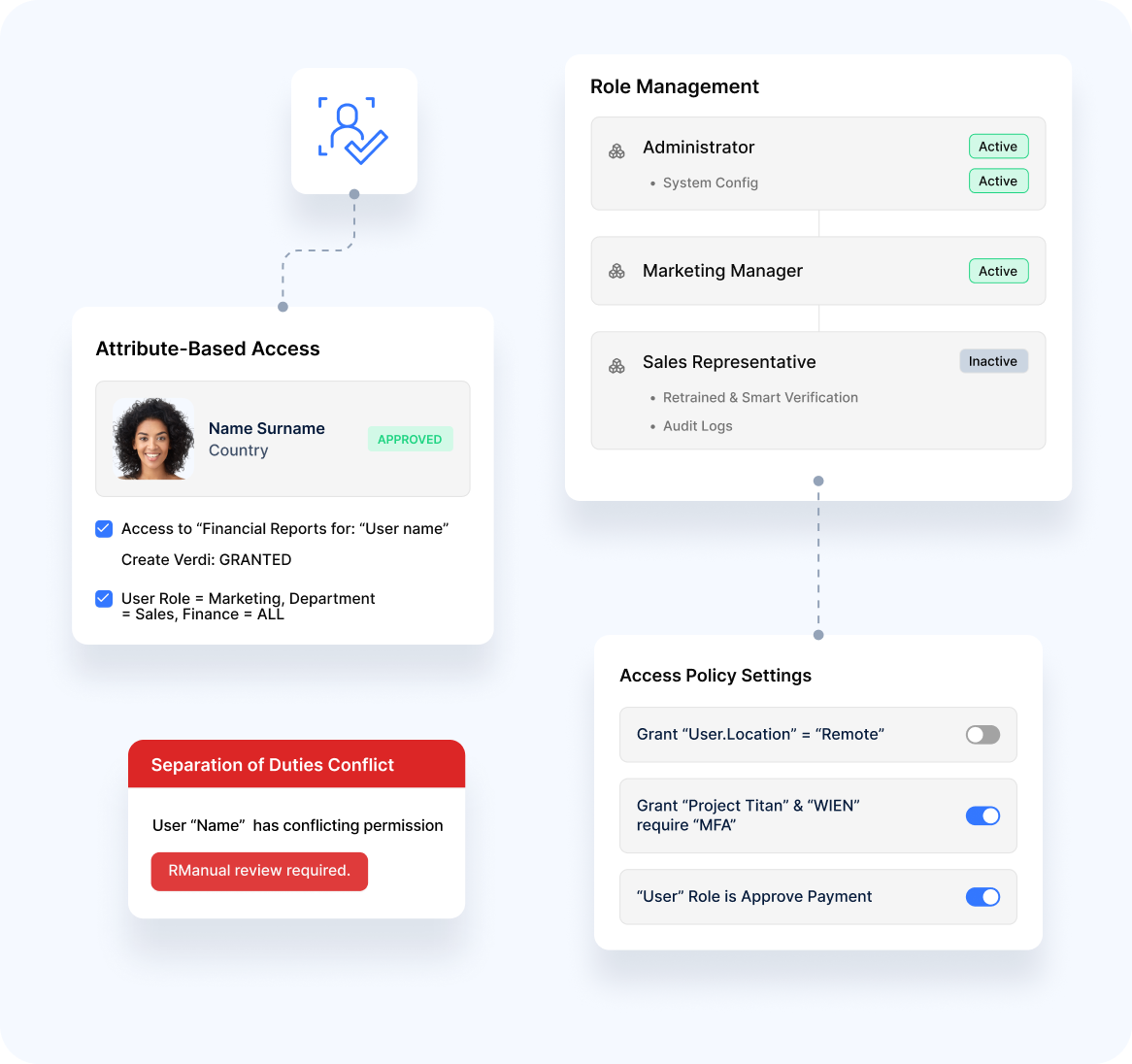
Intelligent Access Control
Our solution delivers sophisticated resource protection:
Smart Safeguards
- Role-Based Access ControlPermission assignment based on organizational roles
- Attribute-Based PoliciesAccess decisions using multiple identity characteristics
- Dynamic EntitlementsContext-aware permissions that adapt to changing conditions
- Least Privilege EnforcementMinimal access rights based on specific requirements
- Separation of DutiesPrevention of conflicting responsibility combinations
Governance Features
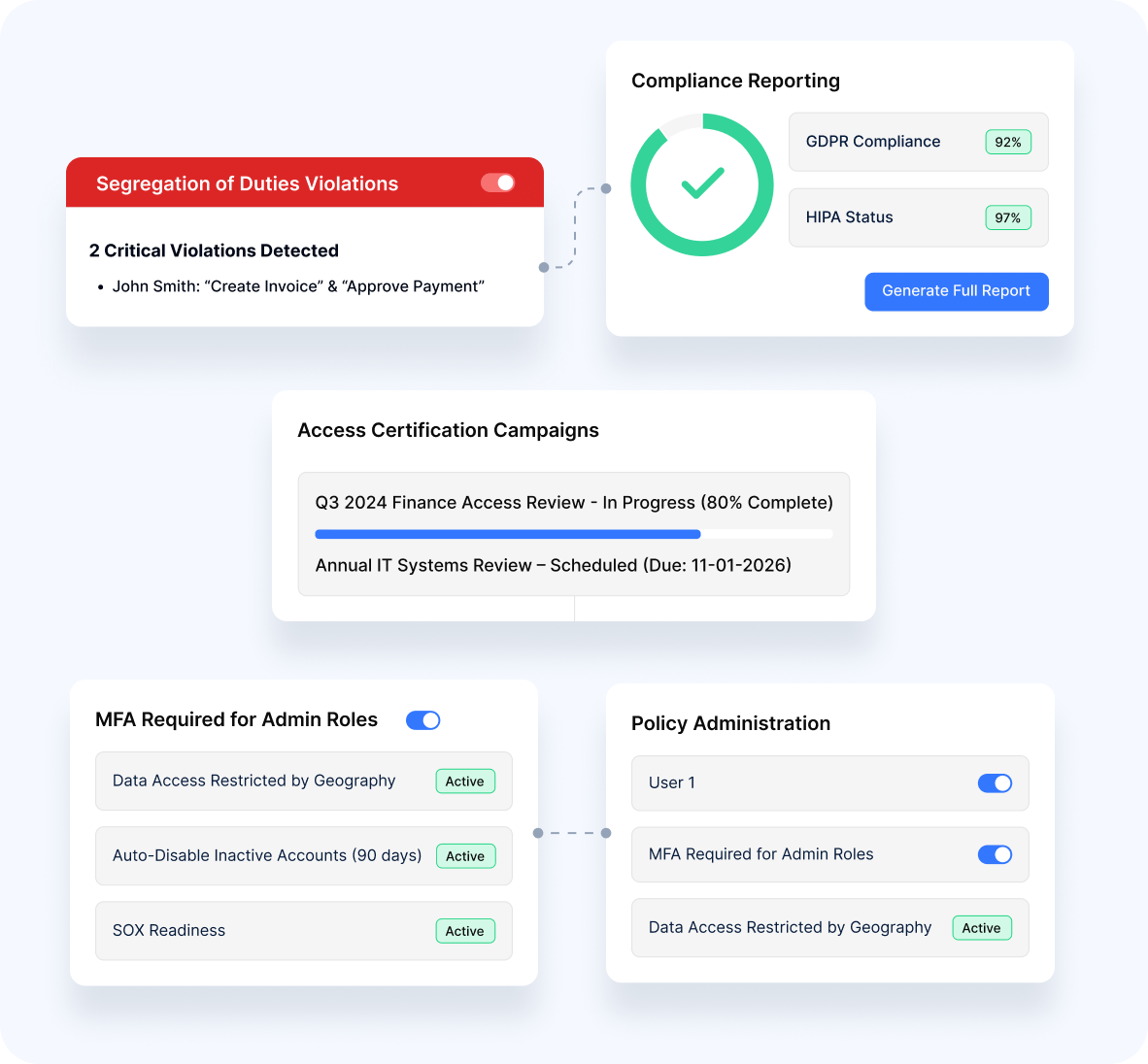
Identity Governance
Our platform enables comprehensive identity oversight:
Identity Control
- Access CertificationPeriodic review and validation of user entitlements
- Policy AdministrationCentralized management of access rules
- Segregation of DutiesEnforcement of responsibility separation
- Audit TrailDetailed logging of identity and access activities
- Compliance ReportingDocumentation to support regulatory requirements
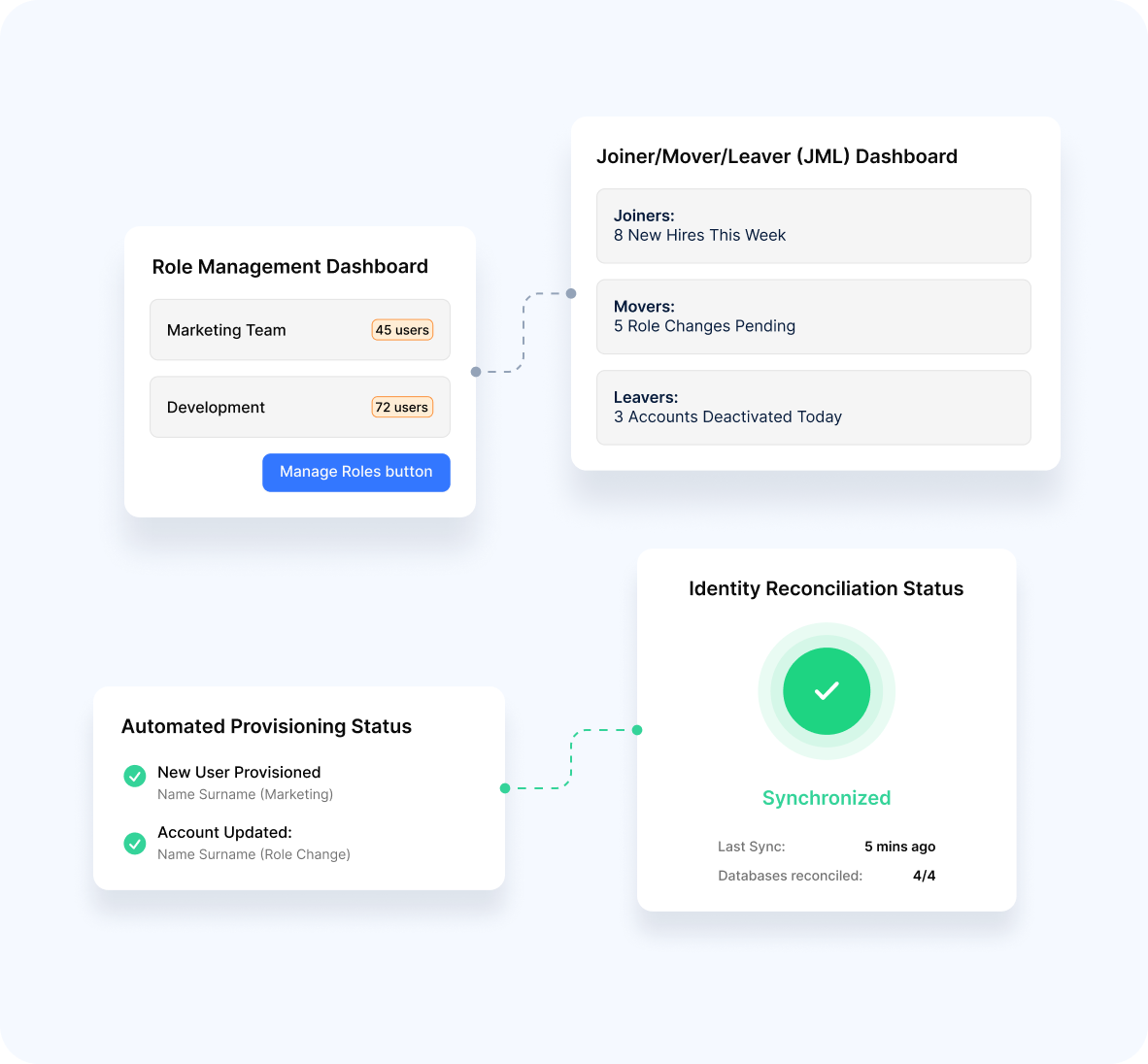
Lifecycle Management
- Automated ProvisioningStreamlined account creation and entitlement assignment
- Role ManagementAdministration of organizational roles and associated permissions
- Access Request WorkflowsStructured processes for permission changes
- Joiner/Mover/Leaver HandlingEfficient management of organizational changes
- Identity ReconciliationSynchronization across multiple systems
Authentication & Authorization

Flexible Authentication
Our platform supports diverse verification methods:
Versatile Verification
- Multi-Factor OptionsCombination of multiple authentication elements including passwordless authentication
- Biometric IntegrationFacial recognition for strong identity verification
- Adaptive AuthenticationSecurity appropriate to access risk
- Single Sign-OnUnified authentication across multiple applications
- Social Identity FederationIntegration with external identity providers
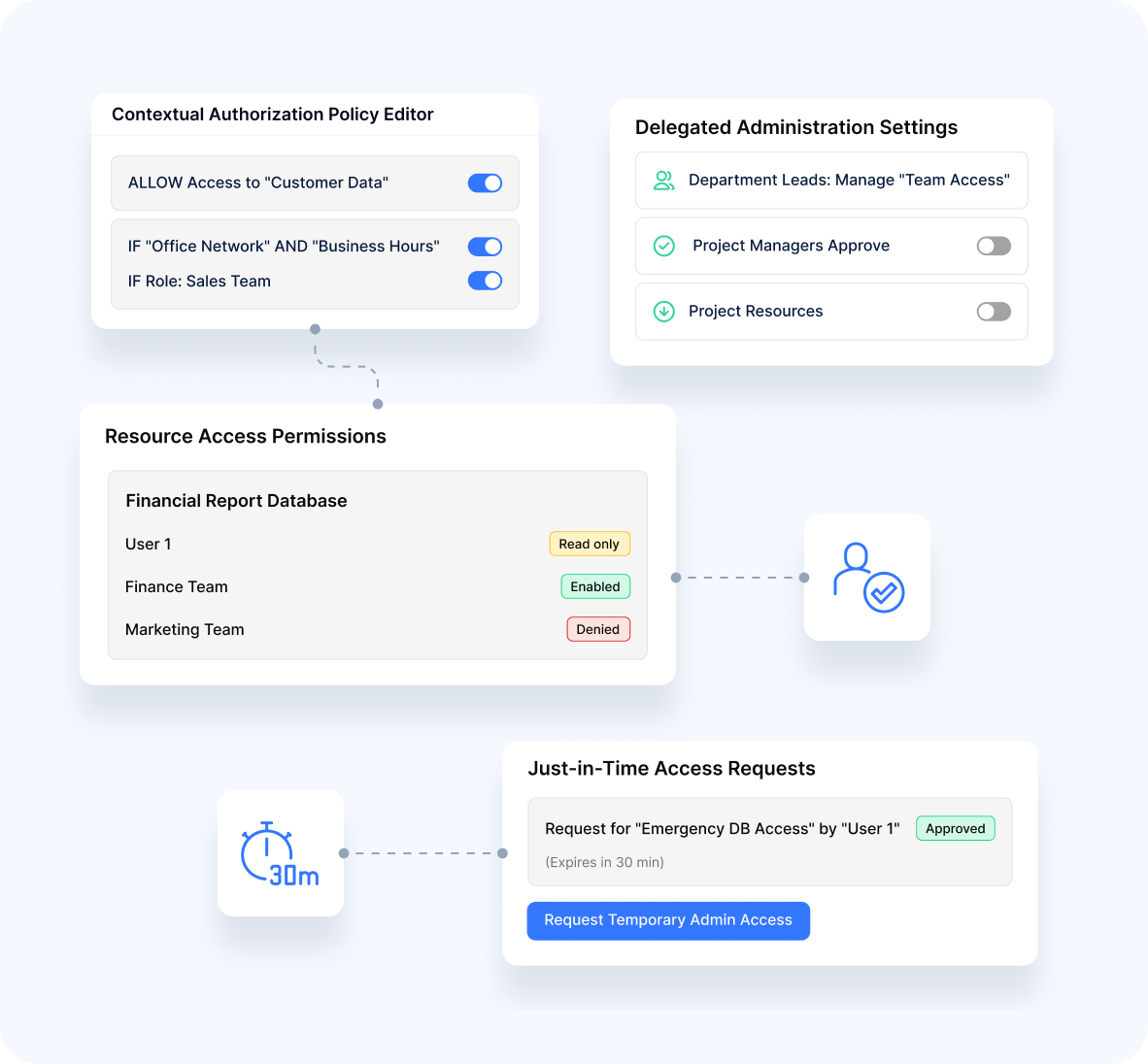
Fine-Grained Authorization
- Contextual AuthorizationAccess decisions based on environmental factors
- Resource-Level PermissionsGranular control over specific system elements
- Policy-Based AccessRule-driven authorization for consistent enforcement
- Just-in-Time AccessTemporary elevation of privileges when required
- Delegated AdministrationDistributed management of access permissions
Implementation Options
Flexible Deployment
Our platform supports diverse integration approaches:
REST API Integration
- Programmatic access to identity and access functions
Standards Support
- Alignment with OAuth 2.0, OIDC, SAML, and other frameworks
SDK Implementation
- Development libraries for custom integration
Pre-Built Connectors
- Ready-made integration with common applications
Identity Gateway
- Protection for legacy applications
Enterprise Readiness
Our solution meets the needs of complex organizations:
Multi-Tenant Architecture
- Support for diverse organizational structures
High Availability Design
- Reliable operation for critical identity services
Scalability
- Capacity to handle growing user and application volumes
Performance Optimization
- Efficient operation for access-intensive environments
Hybrid Identity Support
- Management across cloud and on-premise systems
Security Features
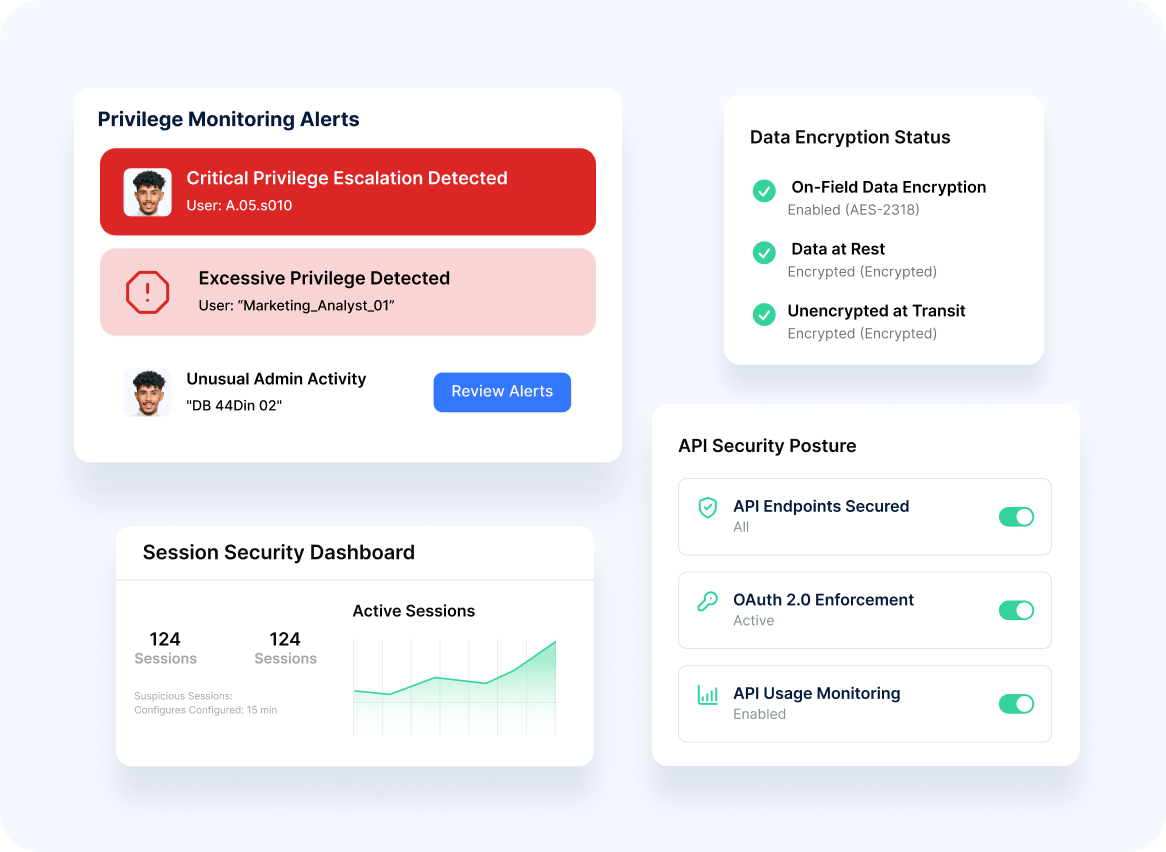
- Comprehensive Protection
- Risk Management
Our platform implements robust security measures:
- Encryption Protection of sensitive identity data
- Session Security Safeguards for authenticated user sessions
- Privilege Monitoring Detection of excessive or unusual permissions
- Threat Protection Defense against common identity-related attacks
- API Security Protection of identity service interfaces
Our solution incorporates sophisticated risk controls:
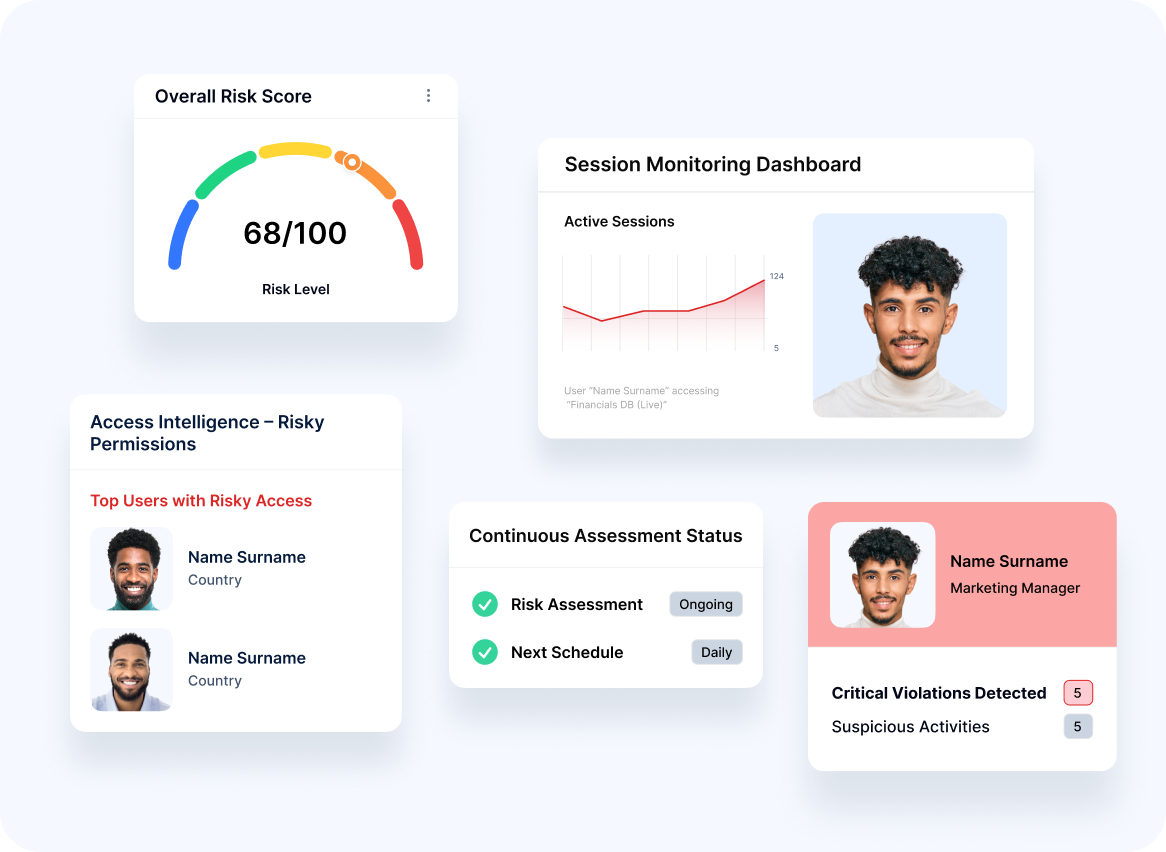
Access Intelligence
Analytics to identify risky permission combinations
Anomaly Detection
Identification of unusual access patterns
Session Monitoring
Oversight of authenticated user activities
Risk-Based Access Policies
Authorization rules based on risk factors
Continuous Assessment:
Ongoing evaluation of identity and access risks

Advantage
Our identity access management capabilities deliver distinctive benefits:
Unified Identity Approach
Seamless connection between verification and access management
Balanced Security Model
Strong protection without excessive complexity
Modern Architecture
Contemporary design based on industry standards
Integration with Verification
Connection with broader identity validation ecosystem
Regional Expertise
Understanding of MEA-specific identity governance requirements
Transform you IAM with uqudo's comprehensive Identity & Access Management solution.
To discuss implementation options tailored to your organization's needs.
Privacy Overview
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-advertisement | 1 year | Advertisement cookies are used to provide visitors with relevant ads and marketing campaigns. These cookies track visitors across websites and collect information to provide customized ads. |
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |

Please wait while you are redirected to the right page...