Transaction Monitoring
Detect and Prevent Financial Crime with Intelligent Transaction Monitoring
Stay ahead of evolving financial crime threats with uqudo’s powerful transaction monitoring platform.
Why Leading Financial Institutions Choose uqudo's Transaction Monitoring
Reduce False Positives
Cut alert noise by up to 95% with intelligent risk scoring and contextual analysis
Respond in Real-Time
Identify and stop suspicious transactions before they're completed with millisecond processing
Ensure Regulatory Compliance
Meet AML, CFT, and fraud prevention requirements across MENA jurisdictions
Increase Investigation Efficiency
Transform alert management with intuitive case workflows and unified data
Adapt to Emerging Threats
Deploy new detection rules in minutes with no-code rule builder
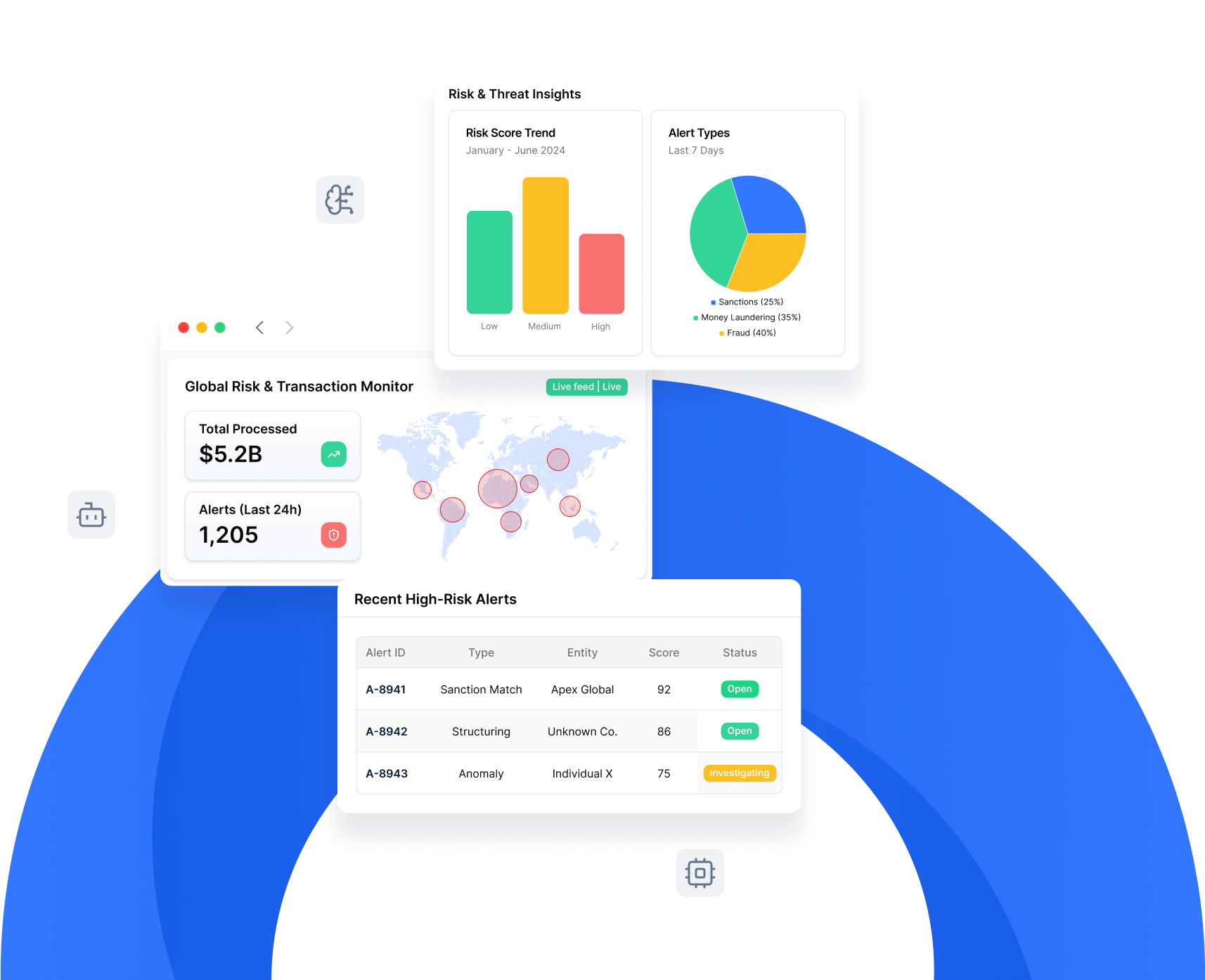
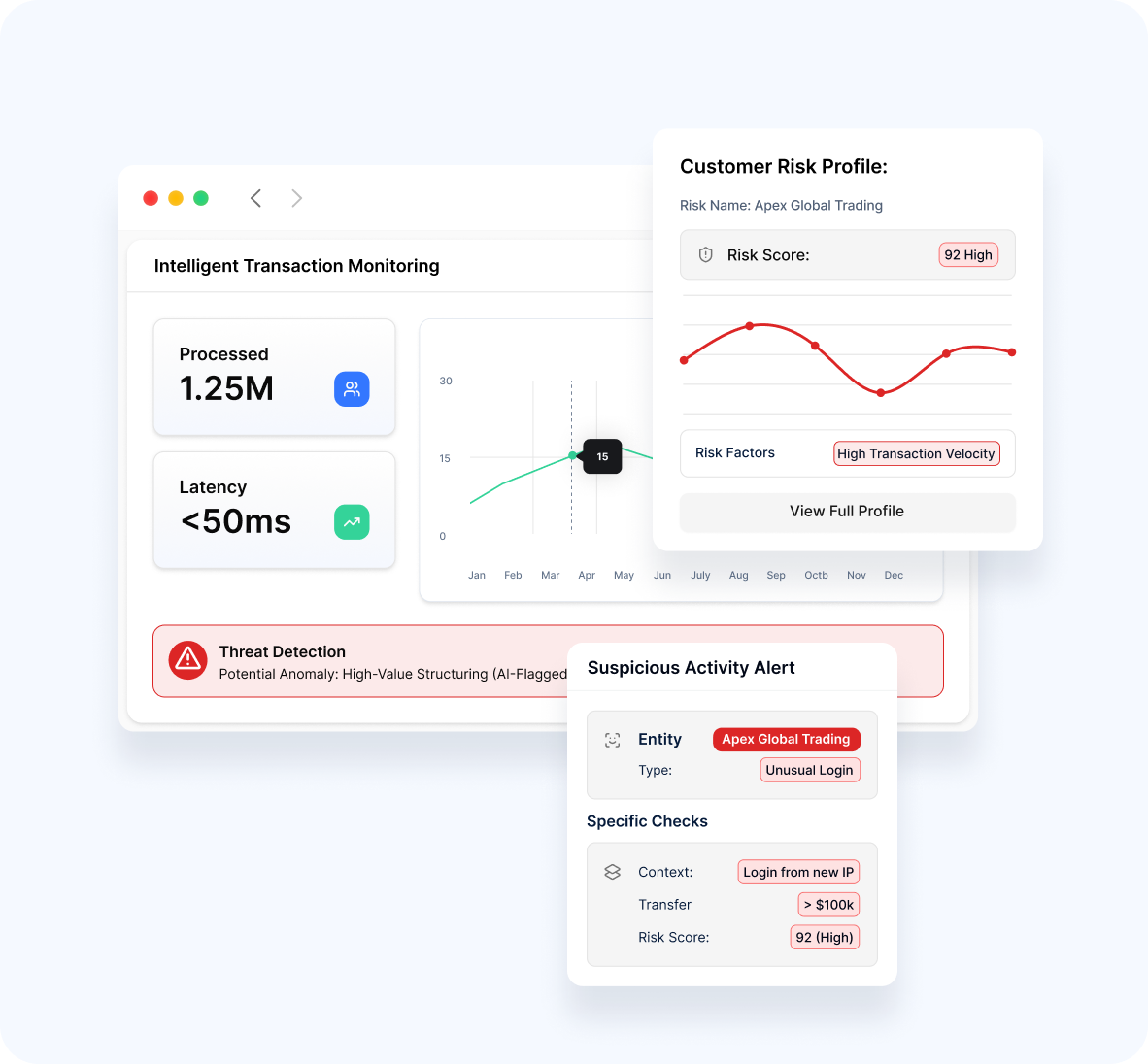
Identify Suspicious Patterns with Intelligent Monitoring & Detection
Deploy sophisticated monitoring software that transform transaction data into meaningful insights.
- Process millions of transactions with minimal latency
- Apply contextual analysis to detect anomalous behavior
- Leverage AI to identify patterns invisible to traditional rules
- Create holistic customer risk profiles based on transaction history
- Deploy both real-time and post-transaction monitoring strategies
Configure Powerful Detection with No-Code Rule Builder
Create and modify detection scenarios without coding expertise, enabling rapid response to new threats.
- Build sophisticated rules through an intuitive interface
- Test rules in sandbox environments with production data
- Deploy new rules in minutes, not weeks or months
- Maintain rule libraries with version control
- Continuously optimize rules with performance analytics

Streamline Investigations with Advanced Case Management
Transform how your team handles alerts with purpose-built investigation tools and workflows.
- Consolidate all case data in a unified interface
- Create efficient workflows with automated routing
- View complete 360° customer profiles during investigations
- Document findings with structured evidence collection
- Generate and submit regulatory reports with a few clicks

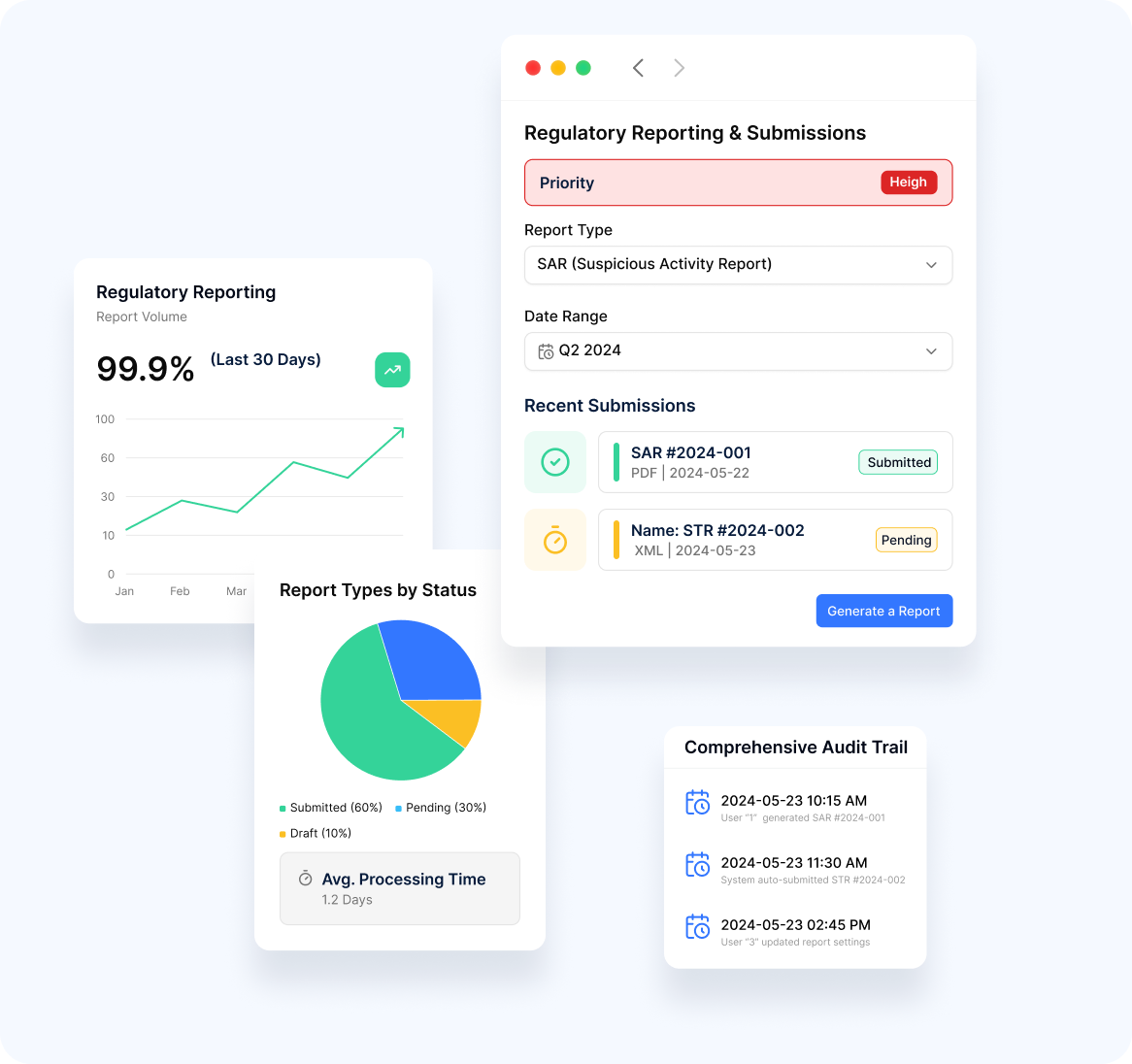
Generate Comprehensive Reports for Regulatory Oversight
Meet reporting obligations with automated, accurate regulatory filings and internal metrics.
- Create Suspicious Transaction Reports (STRs) and Suspicious Activity Reports (SARs)
- Generate required regulatory submissions in proper formats
- Track key performance indicators through intuitive dashboards
- Monitor system and team performance with operational reports
- Maintain comprehensive audit trails for regulatory examinations
Advanced Monitoring Capabilities
- Pragmatic AI-Assisted Insights
- Risk-Based Approach
- Multi-Layered Detection


Enhance traditional rule-based detection with sophisticated AI technologies.
- Identify complex patterns invisible to conventional rules
- Reduce false positives through better risk scoring
- Uncover networks and relationships between entities
- Adapt to changing behaviors with machine learning
- Apply natural language processing to unstructured data
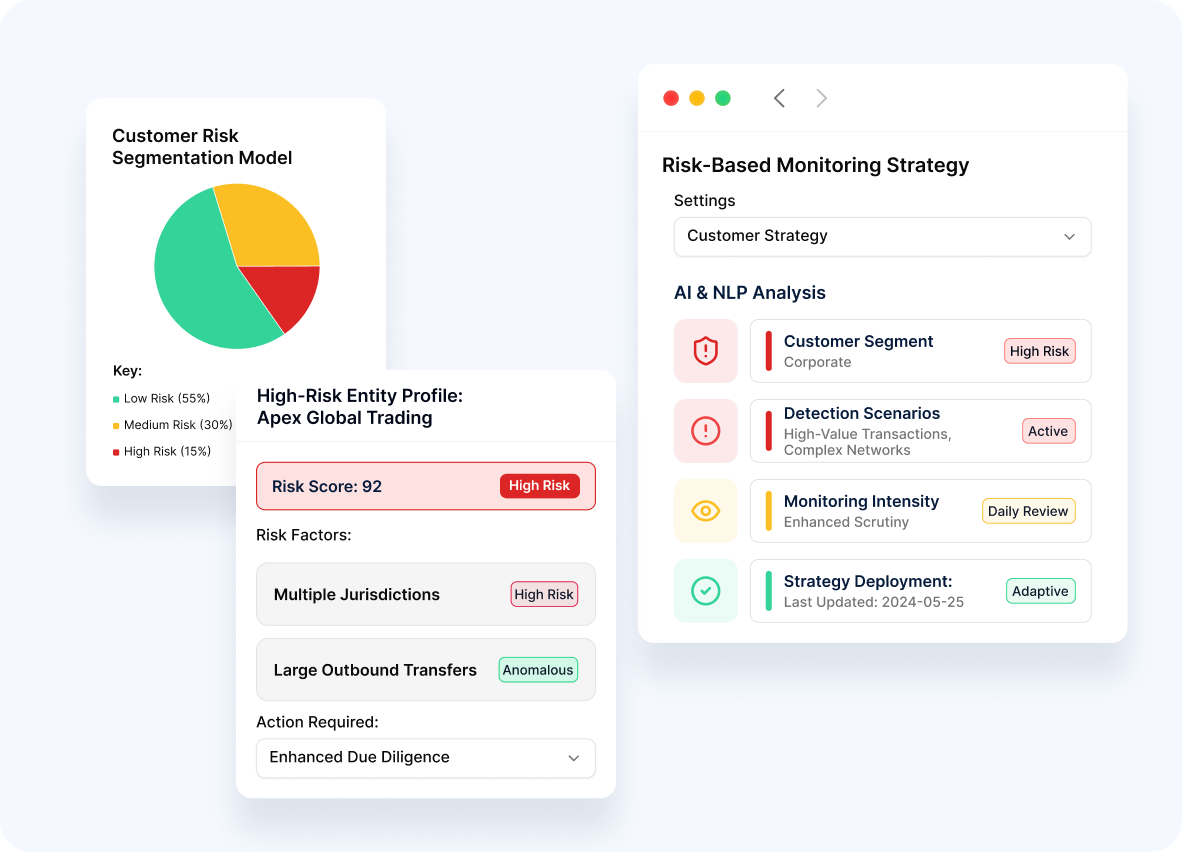
Optimize resource allocation with intelligent risk scoring and segmentation.
- Segment customers based on sophisticated risk models
- Apply appropriate monitoring intensity based on risk level
- Customize approaches for different lines of business
- Identify truly high-risk entities requiring enhanced scrutiny
- Deploy adaptive strategies as risk profiles evolve
Implement a defense-in-depth strategy with complementary detection methods.
- Apply both threshold and behavioral monitoring techniques
- Combine traditional rules with AI and machine learning
- Monitor at the customer, account, and transaction levels
- Deploy network analysis to identify collusion and connected parties
- Implement scenario-specific detection models for various typologies
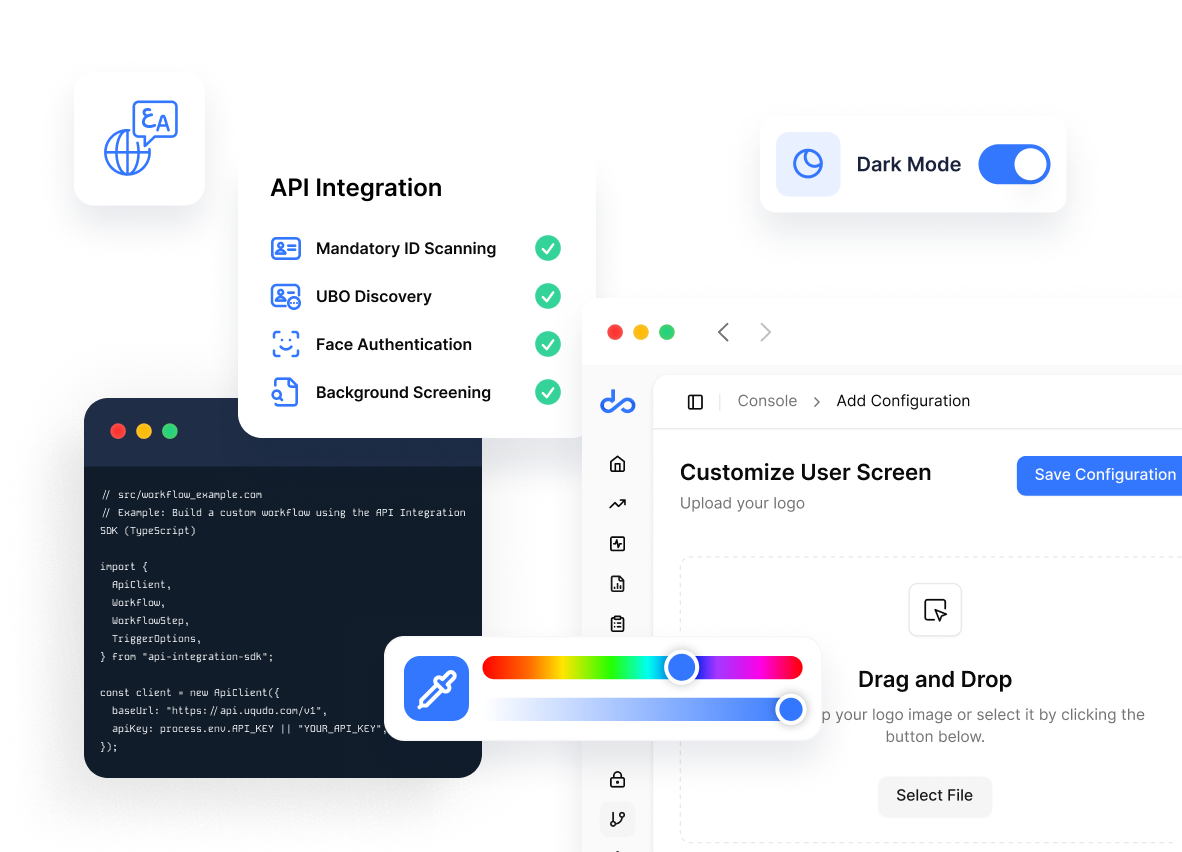
Flexible deployment models for any business need
Choose the integration method that works best for your organization:
-
API IntegrationBuild custom workflows through our comprehensive REST API
-
Custom ApplicationWe design the workflow and the UI to meet your requirements
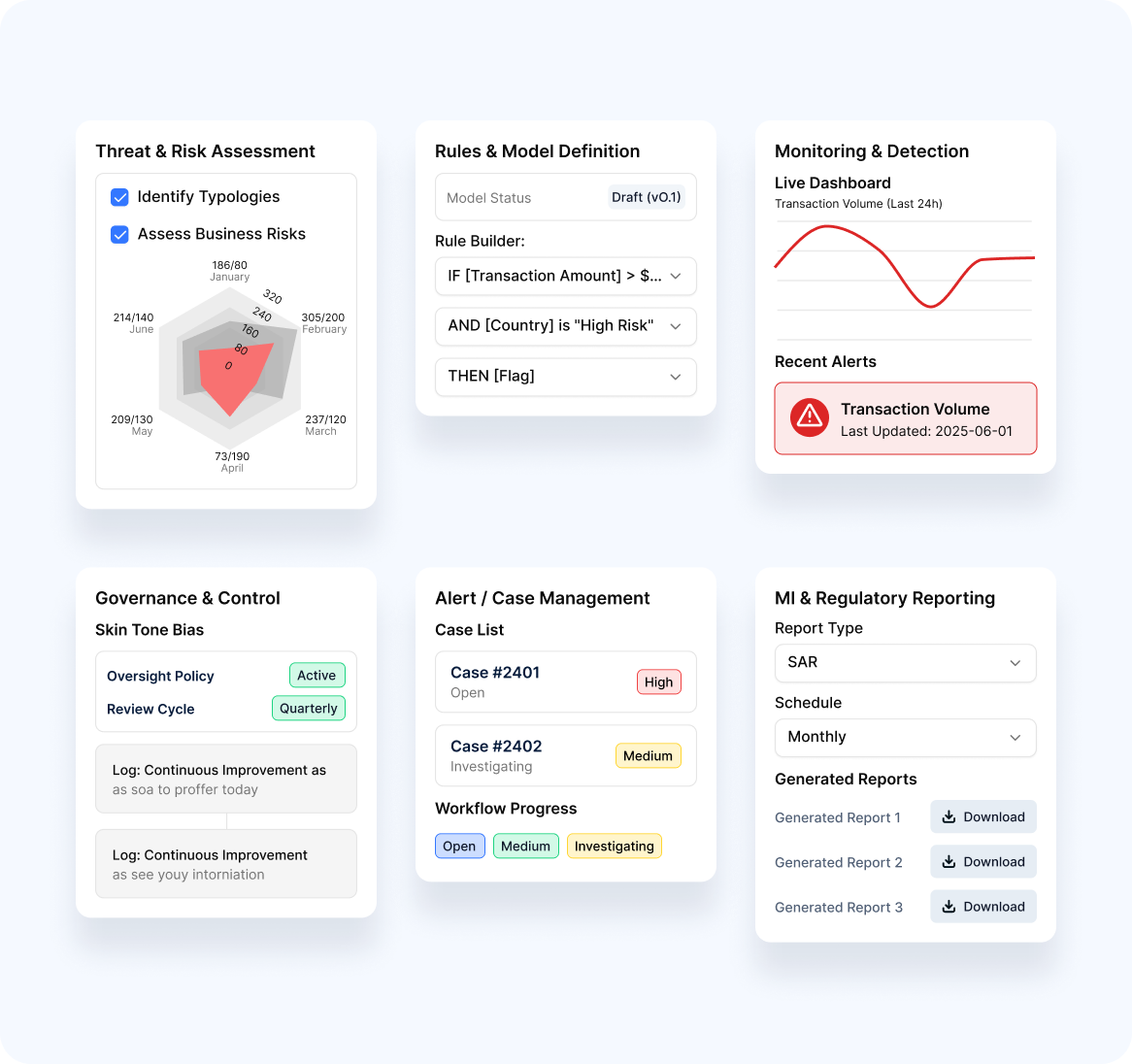
Delivery Methodology
Our structured deployment methodology ensures successful implementation
-
1
Threat & Risk Assessment
Identify specific typologies and risks relevant to your business
-
2
Rules & Model Definition
Design custom rules and models aligned to your risk profile
-
3
Monitoring & Detection
Implement real-time and post-transaction monitoring
-
4
Governance & Control
Establish oversight and continuous improvement processes
-
5
Alert/Case Management
Configure efficient investigation workflows
-
6
MI & Regulatory Reporting
set up required regulatory and management reporting
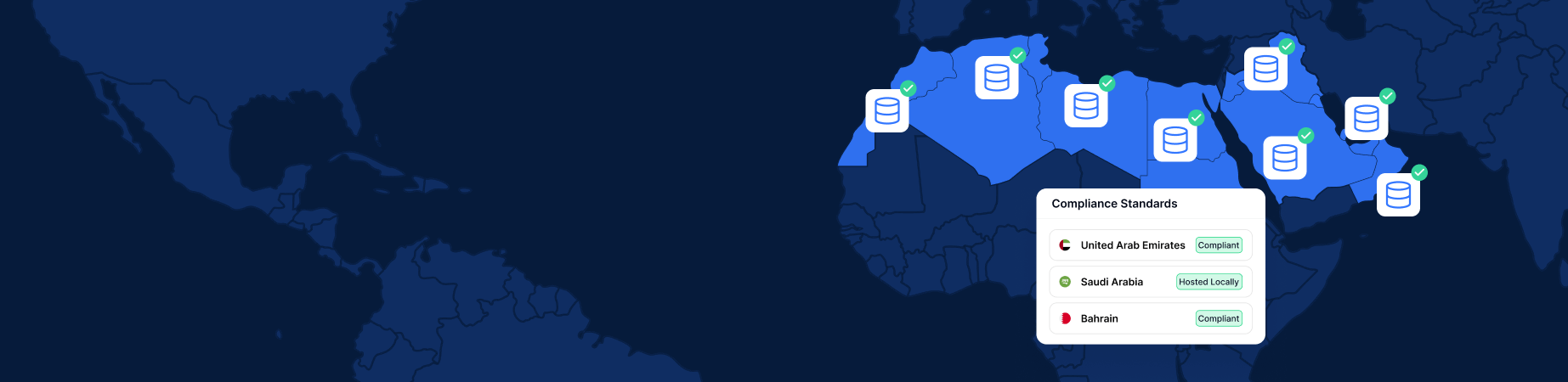
Meet stringent data residency
requirements across MENA
Privacy Overview
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-advertisement | 1 year | Advertisement cookies are used to provide visitors with relevant ads and marketing campaigns. These cookies track visitors across websites and collect information to provide customized ads. |
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |

Please wait while you are redirected to the right page...






