Banking & Financial Services
Stolen and synthetic identities enable account takeovers, transaction fraud, and financial loss.
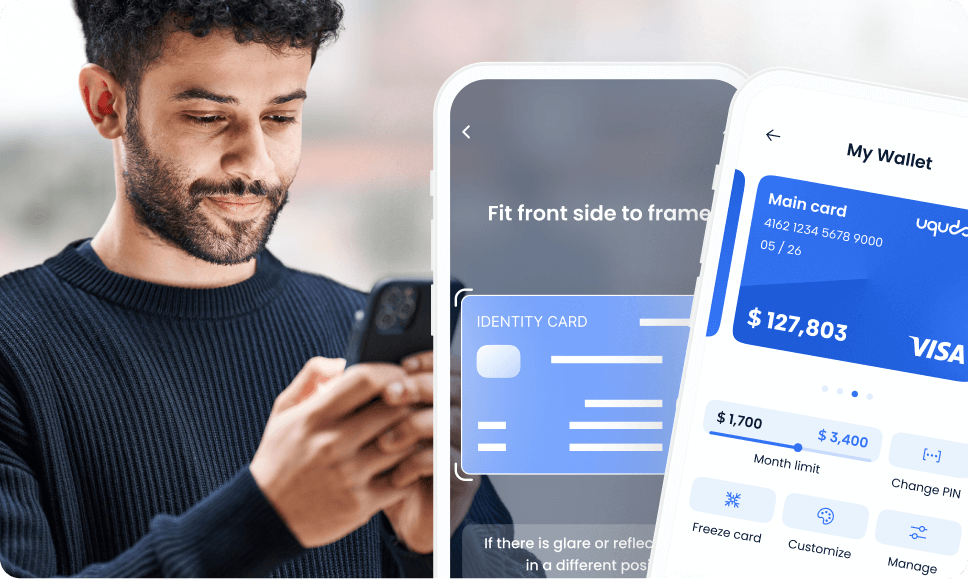
Compliant KYC solution with the regulations of the Central Bank of the UAE, DIFC, and ADGM across licensed financial institution use cases in the UAE
Fraud
AI-powered fraud prevention built for MEA. Cut fraud losses 20-30% and false positives 50-70%.











Four complementary fraud detection layers working together, stopping fraud at every touchpoint while maintaining frictionless experiences for legitimate users.
Fingerprint and trust every device
Detect anomalies in real time
Authenticate identity, not credentials
Screen and block suspicious activity
prevent duplicate accounts by Real-time facial recognition against your entire user database
Persistent device fingerprinting with 99.7% accuracy that detect fraud rings using shared devices
Continuous behavioral analysis comparing typing patterns, swipe gestures, navigation paths, and session behavior against established user profiles
AI-powered transaction analysis with pre-configured MEA fraud rules plus ML anomaly detection, block suspicious payments before they complete




Device fingerprinting creates persistent identity that survives resets and app reinstalls. 160+ signals analyzed in real-time to calculate risk scores and reveal fraud rings through device network graphs
Baseline behavioural profiles established over 3-5 sessions track keystroke dynamics, swipe patterns, and navigation paths. Anomaly detection compares current behaviour against historical profiles to identify unauthorized users and bots
1:N face search against your entire user database identifies duplicate accounts and known fraudsters in real-time. Combined with blacklist screening, liveness detection, and repeat document detection to block fraudulent account creation
Pre-configured MEA fraud rules combined with ML anomaly detection analyze spending behaviour against customer profiles and peer groups. Real-time risk scoring with automated decisioning blocks or holds suspicious transactions for review





Purpose-built for MEA documents, languages, regulations, and fraud patterns with flexible deployment options.
Stolen and synthetic identities enable account takeovers, transaction fraud, and financial loss.

SIM swaps, unauthorized registrations, and subscriber impersonation undermine network and user trust.

Concealed sender and recipient identities expose platforms to mule networks and sanctions risk.

Fraudulent credit access, deliberate defaults, and multi-accounting drain provider revenue rapidly.
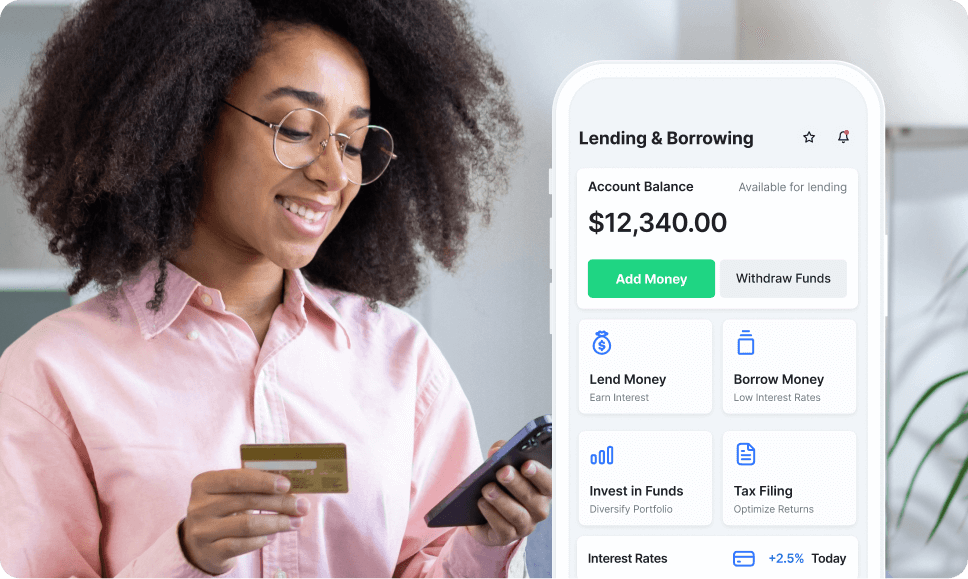
loan stacking, and deliberate defaults surface when identities go unverified.

Concealed ownership, illicit asset movement, and withdrawal fraud exploit weak identity controls.
Account takeovers, wash trading, and unauthorized access thrive behind unverified user identities.
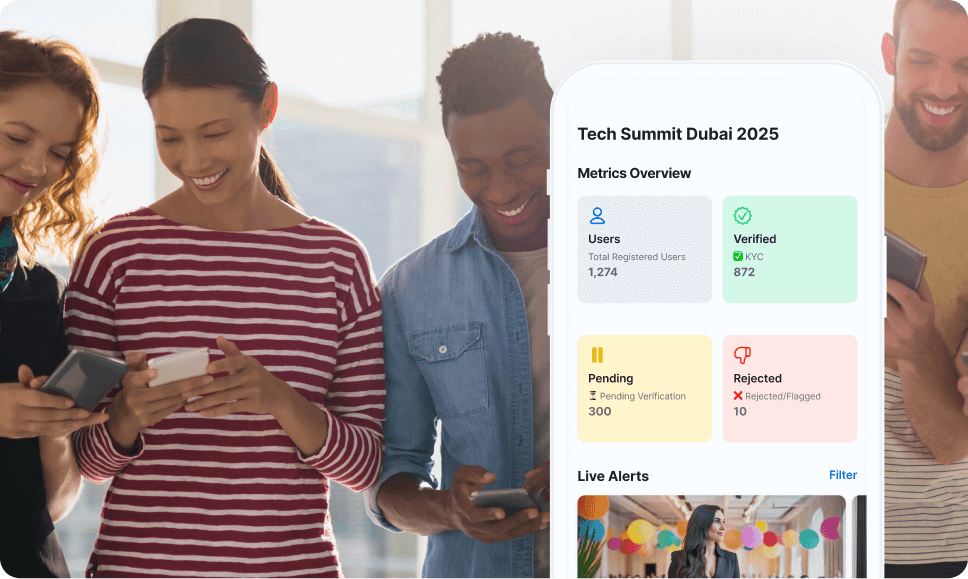
Ticket fraud, duplicate registrations, and unauthorized resale flourish without attendee identity verification.
Chargeback fraud, seller impersonation, and multi-accounting erode platform integrity and user trust.
Impersonation, scam networks, and coordinated abuse scale rapidly without verified user identities.
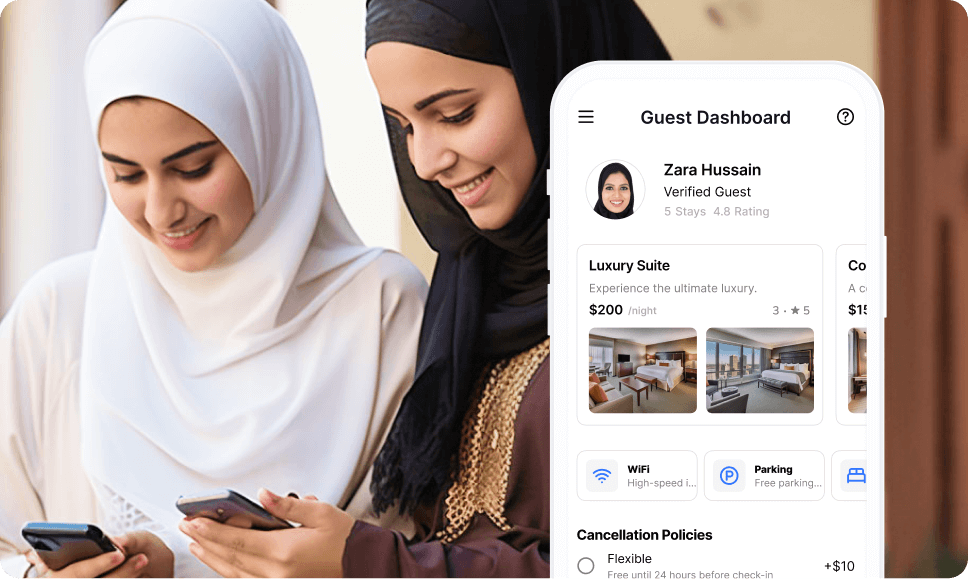
Booking fraud, chargeback abuse, and no-show schemes exploit unverified guest identities.

Fraudulent rentals, liability evasion, and repeat abuse persist when driver identities go unchecked.

Catch fraud that single-method systems miss by forcing attackers to defeat four independent detection layers at once
Each layer compounds detection difficulty exponentially, closing the gaps that fraudsters exploit when organisations rely on one method alone

Stop MEA-specific fraud immediately with detection logic built around regional attack patterns, not retrofitted from other markets
Only fraud platform shipping with pre-trained rules calibrated to GCC and broader MEA threat landscapes out of the box

Stop fraud without frustrating legitimate customers. Fewer false positives mean fewer complaints, fewer support tickets, and higher conversion.
Risk-proportionate friction that protects revenue by reserving visible security steps for genuinely suspicious sessions only

Fraudsters cannot escape detection by resetting devices or switching tools. Identity follows the device, not the session.
One of the largest commercial device networks available, turning every fraud attempt into intelligence that strengthens future detection

Eliminate entire fraud rings, not just individual accounts. Every connection uncovered multiplies prevention impact across your portfolio.
Graph-based detection that traces relationships between accounts, exposing coordinated operations that transaction-level analysis alone cannot see

Fraud signals from onboarding inform transaction monitoring and vice versa. No blind spots between siloed systems.
One platform replacing multiple point solutions, giving teams complete visibility without the integration overhead of stitching vendors together
UqudoFraud.initialize(apiKey: “your_key”) .enableDeviceIntelligence() .enableBehavioralBiometrics() .setFaceSearchEnabled(true)
curl -X POST https://api.uqudo.io/fraud/analyze -H “Authorization: Bearer TOKEN” -H “Content-Type: application/json” -d ‘{ “user_id”: “user_123”, “device_fingerprint”: “…”, “transaction”: {…} }’
- Response:
{ “risk_score”: 85, “risk_level”: “high”, “signals”: { “device_risk”: “emulator_detected”, “behavioral_anomaly”: true, “face_match”: “duplicate_found” }, “recommendation”: “block” }
- RuleEngine()
.setVelocityChecks(true)
.setAmountThresholds(true)
.setGeolocationFlags(true)
DocumentBuilder()
.setScanDocument(true)
.setNFC(true)
.setFacialRecognition(true)

CEO & Co-Founder Tamara
uqudo, with its user-friendly interface, efficient processes, and responsive team, aligns seamlessly with our dedication to delivering fast, easy, and cost-effective customer authentication experiences. This collaboration fortifies our focus on putting our users first and upholding the highest standards of privacy and security.

VP Ecosystem Cloud Middle East Huawei
Partnering with uqudo will enable Huawei Cloud to offer customers cutting-edge identity verification, contributing to the goal of building a more secure and inclusive digital world.

CEO Rain Crypto
We are thrilled to partner with uqudo to leverage their innovative and secure identity technology into our customer’s onboarding process. By prioritising security and user-friendliness, we aim to make the benefits and opportunities provided by cryptocurrencies more accessible to individuals in the region.

CEO Oman Data Park
Oman Data Park is committed to providing our customers with the latest and most advanced technology solutions. Our partnership with uqudo will help us to further enhance our services and deliver fraud-proof digital identity solutions to our customers in Oman.

CEO Get Equity
After our research, we found uqudo to be by far the best AML provider and we are confident that they will help us push our business forward as we grow.

Founder & CEO FinaMaze
What made us choose Uqudo as our digital identity partner is their clear and fast integration process and the constant availability and efficiency of their support team. The client ID verification and video selfie is user-friendly and convenient making our onboarding process quasi-instant.
Built from the ground up for MEA documents, languages, regulations, and infrastructure not adapted from global templates
Operated national digital ID programs serving 5M+ citizens with proven ability to handle enterprise scale and government requirements
Identity + Fraud + Compliance in one integrated solution, no vendor juggling or finger-pointing
Only provider offering SaaS, private cloud, on-premise, and hybrid options & meet any regulatory or data sovereignty requirement
FAQ section
SDK integration takes 1-2 weeks, API integration similar. Transaction monitoring rules can be configured in days. Full platform deployment: 4-6 weeks including custom rules and analyst training.
SIM swap attacks, coordinated BNPL abuse, crypto exchange manipulation, mule account networks, multi-accounting for promotions, velocity-based structuring, and beneficiary fraud rings common in GCC markets.
Real-time search against millions of faces completes in <1 second. Each customer has isolated database. Configurable similarity thresholds balance false positives vs. fraud detection. Works seamlessly during onboarding and authentication.
Extremely difficult. Our 99.7% persistence survives factory resets, VPNs, privacy tools, and app reinstalls. Even if fraudsters use new devices, behavioral biometrics and 1:N face search provide additional layers.
ML models learn from your specific fraud patterns and legitimate user behavior. Multi-layered approach means we require multiple suspicious signals before triggering high-friction actions. Continuous optimization based on investigation outcomes.
Configurable responses: automatic block, hold for manual review, step-up authentication, or fraud team alert. You control thresholds and actions based on risk appetite. Complete audit trails for investigations.
Yes. Pre-configured MEA rules provide immediate value. You can add custom rules, adjust thresholds, create customer segments with different rules, and integrate proprietary fraud intelligence.
Join 50+ leading enterprises across MEA delivering frictionless, secure onboarding with uqudo.
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-advertisement | 1 year | Advertisement cookies are used to provide visitors with relevant ads and marketing campaigns. These cookies track visitors across websites and collect information to provide customized ads. |
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |

Please wait while you are redirected to the right page...